Cybersecurity Essentials provide a practical, scalable foundation for tech-driven organizations navigating complex digital ecosystems, helping teams anticipate threats, align security with business strategy, and build trust with customers and partners. By embracing cybersecurity best practices, organizations strengthen data protection, safeguard sensitive information, and cultivate a culture of security awareness across all layers of IT and operations. A well-implemented program also reinforces network security by monitoring access, segmenting critical systems, applying least-privilege controls, and reducing attack surfaces across on-premises and cloud environments. With security risk management guiding priorities, leaders can map threats to business impact, allocate resources effectively, and measure progress through clear metrics and governance. This descriptive overview introduces core elements that organizations should tailor to their unique risk profiles, technology stacks, and regulatory requirements.
Viewed through an alternative lens, this topic can be described as digital security foundations that safeguard data, networks, and operations in agile, cloud-first environments. Think in terms of information protection, layered defenses, and governance around risk management, rather than a bare checklist. Focusing on data protection, identity controls, and secure development practices reinforces a resilient security posture that enables responsible innovation. Framing the discussion with related terms such as cybersecurity best practices, data protection, network security, and risk governance helps readers connect concepts to concrete controls.
Cybersecurity Essentials in Practice: Implementing a Data-Driven Security Program
Implementing Cybersecurity Essentials isn’t a one-time checklist; it’s a data-driven security program that aligns with business goals. Start with asset discovery, inventory, and configuration management to gain visibility across on-premises, cloud, and container environments. This visibility underpins data protection by enabling precise classification and encryption decisions, and it strengthens network security by supporting targeted access controls and rapid containment when anomalies arise. By weaving together people, processes, and technology, organizations can translate cyber risk into measurable business outcomes and establish a foundation for ongoing improvement.
Beyond technical controls, governance and security risk management ensure that security investments map to risk, budgets, and performance metrics. Regular risk assessments, a living risk register, and clear ownership help prioritize actions and balance resilience with innovation. Applying zero-trust principles, continuous monitoring, and secure baselines for patch management, access control, and secure software development lifecycle (SSDLC) reinforces cybersecurity best practices while shrinking the blast radius in incident scenarios. Data protection, encryption, and tested backups remain evergreen capabilities that support recoverability and strengthen trust with customers.
Enhancing Resilience with Cybersecurity Best Practices and Network Security
Strengthening resilience relies on practical cybersecurity best practices that permeate daily operations. Enforce strong identity and access management with multi-factor authentication, least-privilege access, and comprehensive logging, and integrate patch management with an emphasis on secure coding during the software development lifecycle. A robust network security posture—encryption, segmentation, firewalls, and intrusion detection—prevents lateral movement and protects data at rest and in transit, forming a concrete extension of the cybersecurity essentials framework.
A mature program also addresses external and third-party risk through vendor risk assessments, secure software supply chain requirements, and ongoing security awareness training. Align governance, risk, and compliance with business objectives to measure security performance, justify investments, and continuously improve data protection, network security, and risk management. Regular incident response drills and tabletop exercises build readiness, helping teams detect, contain, and recover quickly while maintaining customer trust.
Frequently Asked Questions
What are Cybersecurity Essentials, and how do they support data protection and network security in a modern tech-driven business?
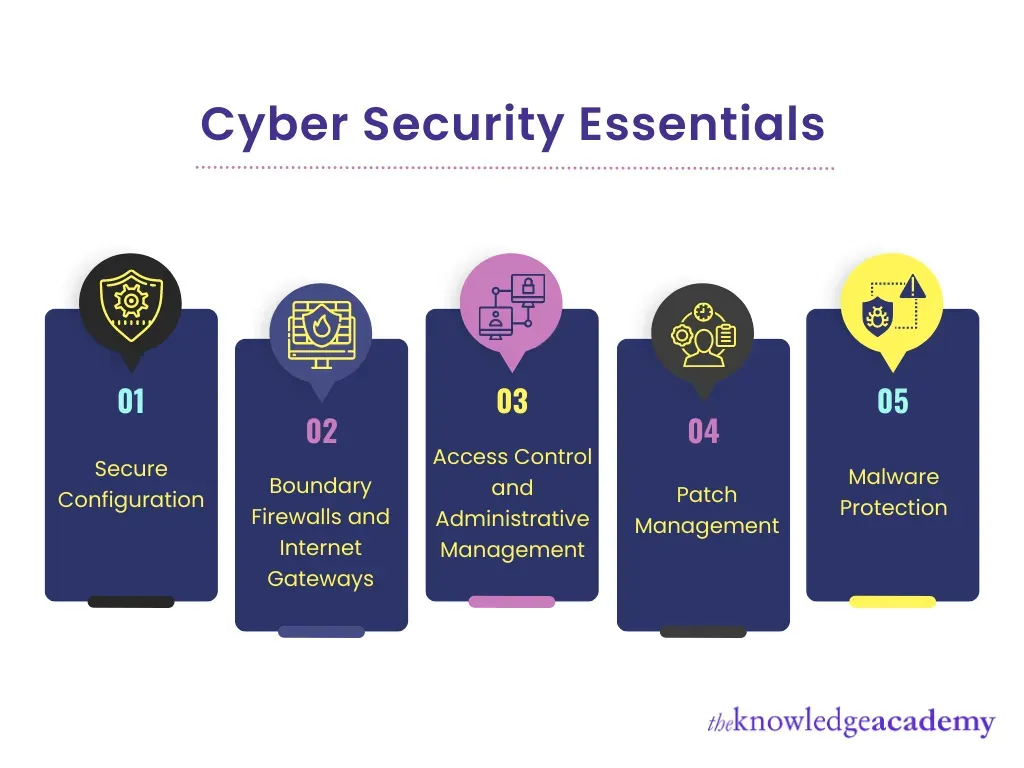
Cybersecurity Essentials are a practical, scalable framework of controls designed to protect data and systems while enabling innovation. They include asset discovery and inventory, access control, patch management, data protection (encryption, data loss prevention, and retention policies), and network security (segmentation, firewalls, and zero-trust). By applying these cybersecurity best practices, organizations strengthen data protection and reduce exposure across cloud and on‑premises environments.
How does security risk management integrate into the Cybersecurity Essentials framework for tech-driven organizations?
Security risk management is the governing layer of the Cybersecurity Essentials. Begin with regular risk assessments to identify threats, vulnerabilities, and consequences, and maintain a risk register to guide prioritization. Align controls with business goals through governance, risk, and compliance (GRC) practices, and tie security initiatives to data protection, network security, and third‑party risk. When decisions follow cybersecurity best practices, the program delivers measurable risk reduction and greater resilience for technology‑driven organizations.
| Section | Key Points | Notes / Relevance |
|---|---|---|
| Introduction | Tech-driven businesses rely on connected systems, cloud services, and rapid development; Cybersecurity Essentials should be practical, scalable, and aligned with business goals. | Sets the stage for why a practical security program matters for modern organizations. |
| Threat Landscape | Threats have evolved to phishing, supply chain attacks, ransomware, and software/IoT exploits; vulnerabilities lie in people, processes, and governance. | Highlights the need for layered, holistic defenses and governance across external, internal, and third-party risks. |
| 1) Asset discovery, inventory, and configuration management | Know what you own; maintain up-to-date inventory of hardware, software, cloud resources, containers, and endpoints; enforce secure baselines; retire obsolete systems. | Foundational for precise controls, rapid response, and data protection. |
| 2) Access control and identity management | Use strong authentication (MFA), enforce least-privilege access, monitor/rotate privileged accounts, and apply identity governance. | Reduces credential theft and limits blast radius during incidents. |
| 3) Patch management and secure software development | Adopt risk-based patching, prioritize high-severity vulnerabilities, apply patches promptly across dev/test/prod; integrate security into the SDLC and practice secure coding. | Prevents known exploits and strengthens software resilience. |
| 4) Data protection and encryption | Classify data, encrypt at rest and in transit, implement DLP, define retention/disposal policies, and test encrypted backups. | Protects sensitive information and supports compliance and recoverability. |
| 5) Network security and segmentation | Deploy firewalls, IDS, segmentation; adopt zero-trust principles; secure remote access via VPN/ZTNA; monitor for suspicious activity. | Limits lateral movement and strengthens perimeters with continuous monitoring. |
| 6) Endpoint protection and incident readiness | Use EPP/EDR, keep devices patched, enforce secure configurations; have an IR plan and regular tabletop exercises. | Improves detection, containment, and recovery capabilities. |
| 7) Security risk management and governance | Conduct regular risk assessments, maintain a risk register, align security with business objectives; use GRC frameworks for oversight. | Connects security programs to business priorities and accountability. |
| 8) Security awareness and culture | Ongoing training, phishing simulations, clear security responsibilities; foster a security-minded culture. | Transforms controls into everyday habits and reduces human risk surface. |
| 9) Third-party risk management | Vendor risk assessments, secure software supply chain requirements, monitor third-party access; enforce least privilege for external connections. | Reduces residual risk from external dependencies and integrations. |
| Practical Implementation Roadmap | Baseline assessment; prioritize by risk; build a security-enabled culture; establish automated controls; test and iterate. | Guides phased rollout and continuous improvement. |
| Benefits of Embracing Cybersecurity Essentials | Enhanced data protection, stronger network security, reduced breach risk, and informed decision-making. | Demonstrates concrete business value and supports responsible innovation. |
| Balancing Security with Innovation | Well-designed Cybersecurity Essentials can accelerate innovation by providing a secure foundation for new services, cloud adoption, and remote work. | Security and speed can co-exist when controls are practical, repeatable, and aligned with business goals. |
Summary
Cybersecurity Essentials are not a one-size-fits-all checklist, but a durable framework that adapts to changing threats and business needs. By integrating cybersecurity best practices with robust data protection, network security, and security risk management, tech-driven businesses can reduce risk, protect assets, and sustain growth. The most successful programs empower people, processes, and technologies to work together—turning cyber resilience from an abstract concept into a daily, measurable capability. Start with a clear inventory, implement strong access controls, protect data with encryption, and continually test your defenses. With the right foundation, your organization can innovate securely and maintain trust in an increasingly digital world.